Hi @ Jakub Śliwiński,
Welcome to Microsoft Q&A Platform.
It looks like your P2S gateway deployment is failing validation, usually because of one of two things: a mis-matched Azure AD auth block or an unsupported gateway SKU. Here’s a quick checklist to get you un-blocked:
Grab the “Inner Errors” :
In the Azure portal go to your resource group → Deployments.---> Click on the failed deployment (Microsoft.Network-…) → Details or JSON view → expand properties.error.details.
That section will show you exactly which parameter or value is invalid.
You can also run:
az group deployment show \ --name Microsoft.Network-… \ --resource-group
and inspect the .error.details object.
Confirm your gateway SKU & VPN type:
- Point-to-site with OpenVPN (SSL) + Azure AD auth requires a Standard-family SKU (VpnGw1 or above) and RouteBased VPN type. • Basic SKU only supports IKEv2/cert auth, so if you accidentally deployed Basic, the template will reject the OpenVPN+AAD block.
- If you need to upgrade, recreate or scale your gateway to VpnGw1+ (you can’t swap a Basic SKU in place).
- Verify your Entra ID settings exactly match the App registration Field What to enter Tenant
- Your Directory (tenant) ID GUID only – not the full login URL Audience
- The “Application ID URI” you set under Expose an API (for example api://), not just the 8-digit app object ID Issuer https://sts.windows.net//(with the trailing slash)
- No extra spaces or line-breaks – paste them directly from the App’s Overview/Expose an API pages. • If you’re not sure, open your App Registration in Azure AD, copy the Directory ID, the exact App-ID URI, and the sts.windows.net URL, then paste them into the P2S config.
Re-deploy Once your SKU and auth settings are corrected, hit Save again. The template validation should pass and your P2S profile will generate successfully.
Here is the Issuer Format as per Microsoft Docs
Issuer: URL of the Secure Token Service. Include a trailing slash at the end of the Issuer value. Otherwise, the connection might fail. Example:- https://sts.windows.net/{Microsoft ID Entra Tenant ID}/
Tenant: TenantID for the Microsoft Entra ID tenant. Enter the tenant ID that corresponds to your configuration. Make sure the Tenant URL doesn't have a \ (backslash) at the end. Forward slash is permissible.
- Azure Public:
https://login.microsoftonline.com/{TenantID}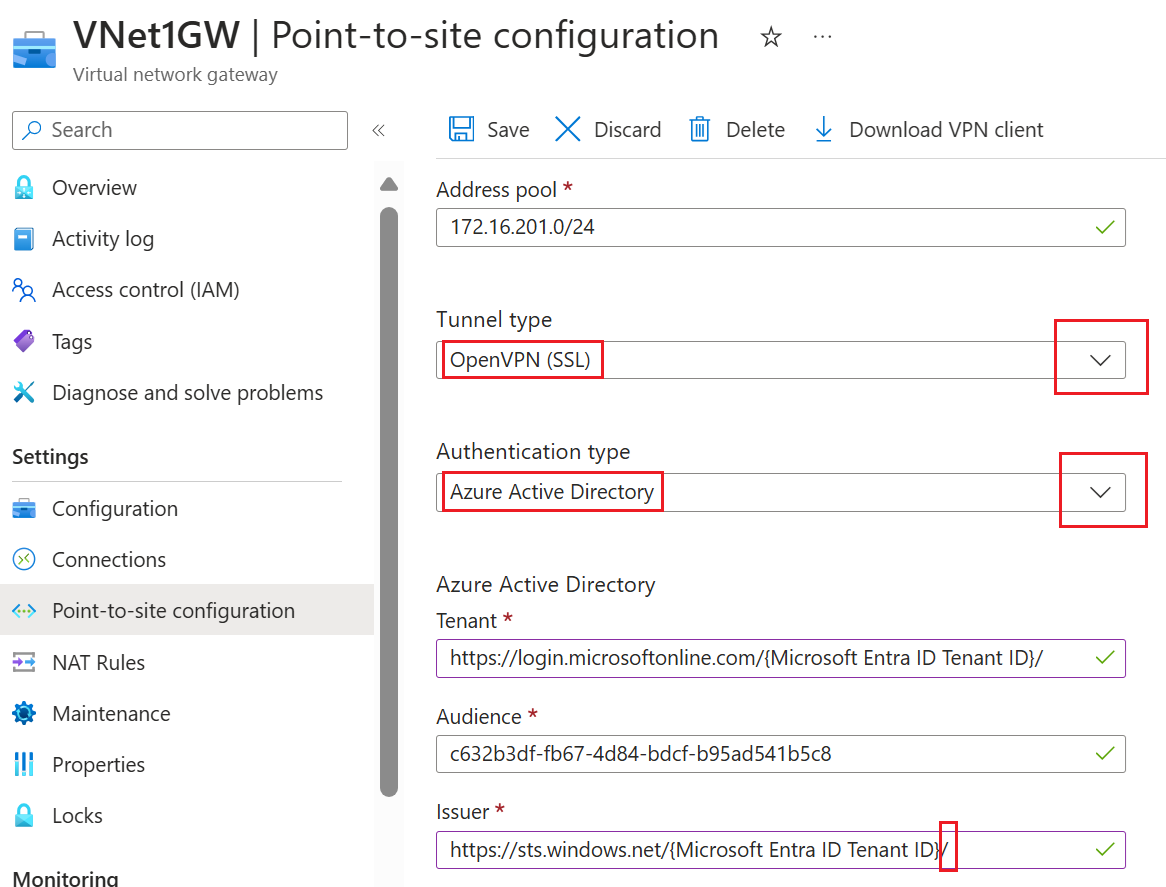
Please and “up-vote” wherever the information provided helps you, this can be beneficial to other community members.
and “up-vote” wherever the information provided helps you, this can be beneficial to other community members.
 and “up-vote” wherever the information provided helps you, this can be beneficial to other community members.
and “up-vote” wherever the information provided helps you, this can be beneficial to other community members.